Network tokens are issued by the card schemes (Visa, Mastercard, American Express) and represent the underlying card across every merchant. PSP tokens are issued by your payment gateway and only work inside that gateway's vault. Both replace the card number with a safe reference, but network tokens auto-update when a card is reissued — PSP tokens don't. For subscription billing, that difference is worth real money.
Two different things, both called "tokens"#
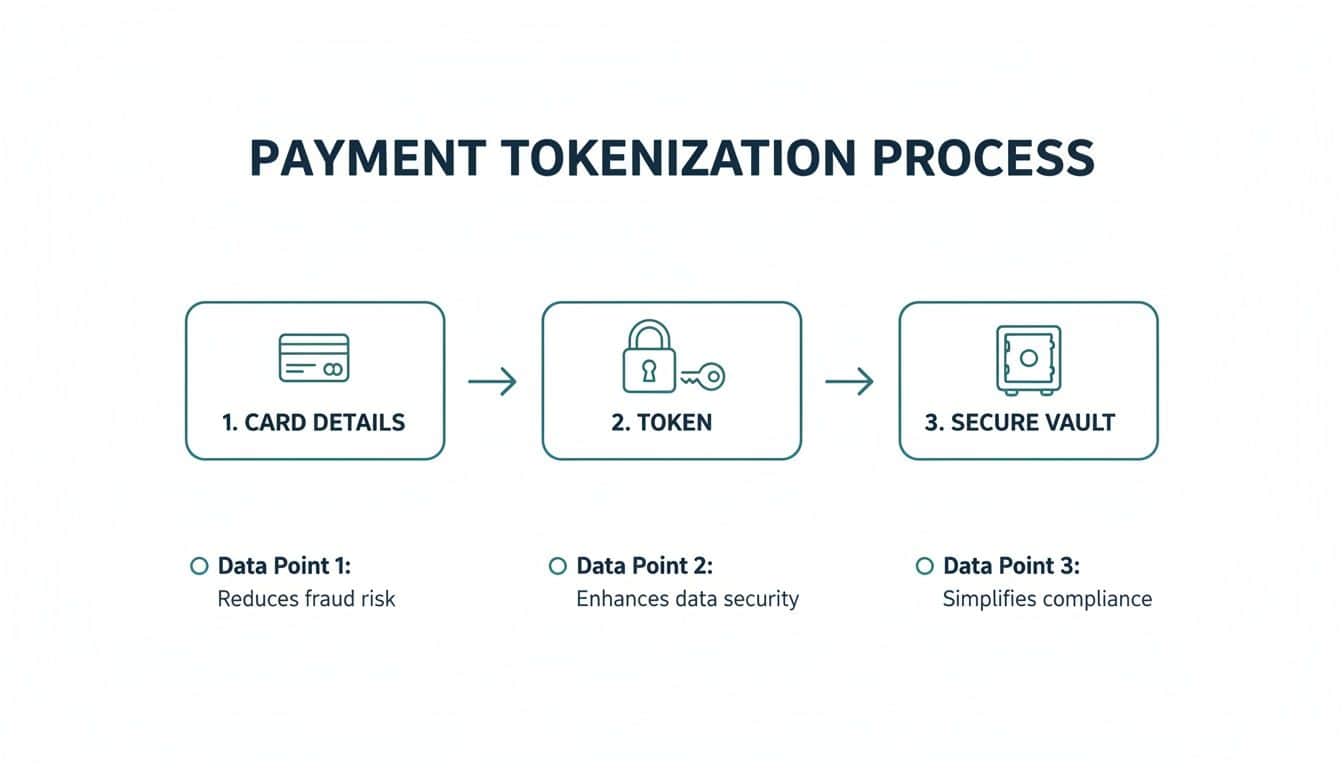
Almost every conversation about payment tokenisation conflates two technologies that work very differently. They both produce a string that stands in for a card number, and both reduce PCI scope, but they come from different places and behave differently when something changes.
A PSP token (sometimes called a vault token, gateway token, or merchant token) is created by your payment processor when you first capture a card. It's stored in their vault and can only be used through that processor. If you switch from Stripe to Braintree, your Stripe tokens are useless on Braintree.
A network token is created by the card scheme itself — Visa Token Service, Mastercard MDES, American Express Token Service. The scheme generates a token tied to the underlying account, and that token can be reused across processors, channels, and devices. The same network token can sit in Apple Pay, in your gateway's vault, and at a physical terminal.
Why network tokens exist#
The schemes built network tokenisation to solve a problem that vault tokens couldn't: card lifecycle. When a customer's card gets reissued — lost, stolen, expired, upgraded — the old PAN dies. If you only had a PSP token, the next charge fails and you're chasing the customer for new details. That's where subscription churn lives.
Network tokens solve this. The token is bound to the account, not the physical card, so when the issuer reissues, the token quietly updates in the background. Your next charge goes through. Visa publishes auth-rate uplift data that suggests this is a meaningful effect for recurring billing — fewer declines, lower involuntary churn.
Comparing options? Book a 15-minute demo — we'll show you a live capture and quote a real number for your call volume.
How they get issued in practice#
You don't request a network token directly. Your gateway does it on your behalf. When you capture a card, the gateway can ask the network to provision a network token alongside the standard authorisation. If the issuer participates (most major UK and US issuers now do), you get back a network token plus a PSP token. The gateway stores both and uses whichever the network prefers at charge time.
The fact that this happens silently is part of why most merchants don't think about it. Your gateway's docs will tell you whether they support network tokens and which schemes they cover. If you're picking a gateway and you do recurring billing, this is one of the questions to ask.
Approval rates and fraud#
Network tokens carry a flag the issuer recognises — the auth comes from a trusted source rather than raw PAN data, which can shift risk scoring in your favour. Reported approval-rate gains run from a couple of percent up to high single digits depending on issuer, geography, and use case. Your mileage will vary.
On the fraud side, both token types remove the PAN from your systems, so neither is "more secure" in the data-breach sense. The difference is operational: if a network token is compromised, the scheme can revoke just that token without invalidating the underlying card. With a PSP token tied to a raw PAN, a compromise often means the customer needs a new card.
What this means if you're choosing a gateway#
Ask three things. Does the gateway issue network tokens for the schemes your customers use? Does it handle the auto-update flow when a card is reissued? Can it report on which charges hit a network token versus a vault token, so you can see the approval-rate lift?
For most Paytia customers, this comes up around recurring payments and stored cards. We integrate with the gateway and store the resulting tokens against the customer — whichever type the gateway gives us. The mechanics of what's a network token and what's a vault token sit one layer down. If you want the vault side covered, we wrote a separate piece on tokenization vaults, and the tokenization glossary entry covers the broader concept.
Both have a role. Network tokens win on lifecycle and approval rates; vault tokens win on flexibility and processor-specific features. A grown-up gateway uses both. Your job is to make sure yours does.
Related reading#
- Pillar guide: What Is Tokenization And How It Secures Your Data
- What Is a Tokenization Vault? A Plain-English Guide
- Tokenisation vs Encryption: What's the Difference?
- POS Tokenisation Explained: How Card Tokens Work at the Till
Comparing options? Book a 15-minute demo — we'll show you a live capture and quote a real number for your call volume.