Encryption scrambles data so that anyone with the right key can read it again. Tokenisation removes the data and replaces it with a meaningless reference that has no mathematical relationship to the original — you need the vault to look it up. Encryption protects card data in transit. Tokenisation removes card data from your systems entirely. Most modern payment stacks use both.
Two different defences, often confused#
Buyers ask us this question more than almost any other technical one: aren't tokenisation and encryption the same thing? They both make data unreadable to attackers. They both feature in PCI DSS guidance. They both turn 16-digit card numbers into something that looks like gibberish.
But they're solving different problems, and using one when you needed the other is how breaches happen.
How encryption works#
Encryption is a reversible mathematical transformation. You take cleartext (a card number, a password, a message), apply an algorithm with a key, and get ciphertext. Anyone with the matching key can reverse the process and recover the original. AES-256 is the standard for payment data; TLS 1.3 is what protects card numbers in transit between a browser and a server.
The security model: keep the key safe and the ciphertext is useless to attackers. Lose the key and the ciphertext is just data — assuming the algorithm is sound. This is why key management is the hard problem in cryptography. The maths rarely fails. The keys leak.
Comparing options? Book a 15-minute demo — we'll show you a live capture and quote a real number for your call volume.
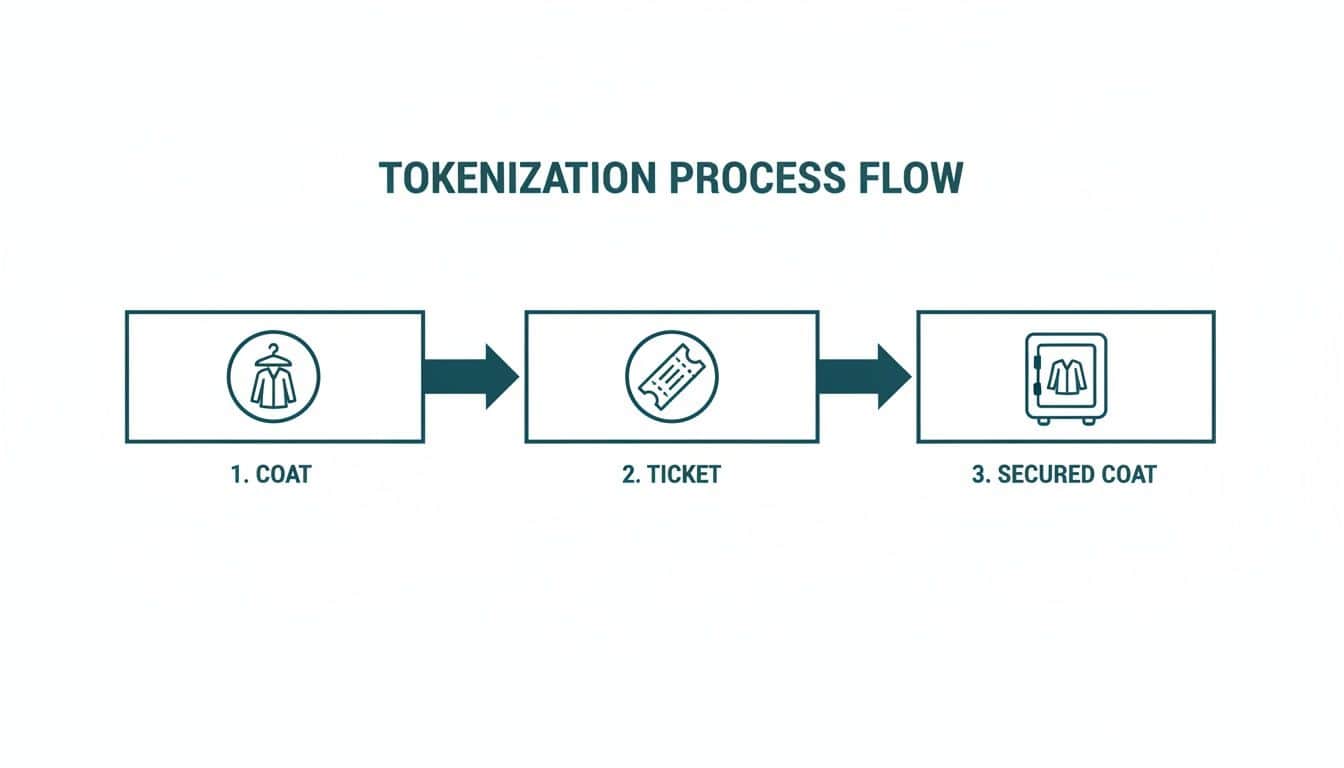
How tokenisation works#
Tokenisation isn't reversible by maths. The token has no mathematical relationship to the underlying card number. You can't decrypt a token because there's nothing to decrypt — the token is a randomly-generated string mapped to the real card inside a separate database called a vault.
To convert a token back to a card number, you have to query the vault and ask. If you don't have access to the vault, the token is meaningless. There's no key recovery, no algorithm to break, no maths to attack. The data simply isn't there.
Where each one belongs#
Encryption protects data when authorised systems still need to read it. A card number travelling from a customer's browser to your gateway has to be readable at the destination — encryption is the right tool. Card data sitting in a backup file that you might genuinely need to restore from one day — encryption with strong key management is the right tool.
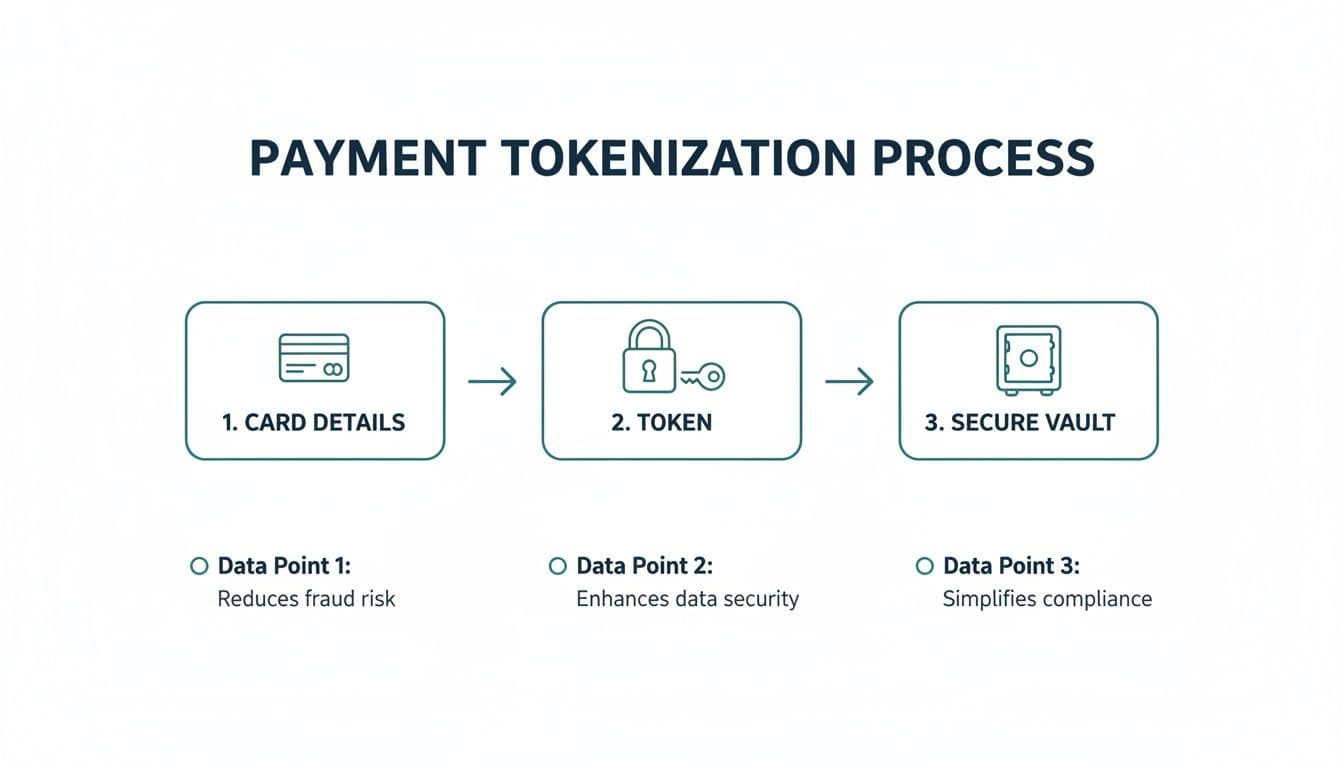
Tokenisation protects data when no system in your environment ever needs the real value again. After a customer's first transaction, your CRM doesn't need the card number — it just needs to identify the card for the next charge. Tokenisation removes the card from your systems entirely so it can't be stolen, leaked, or accidentally logged. PCI DSS treats tokenised systems as out of scope, which is the practical commercial benefit.
Why both, not either#
Real payment flows use both, layered. When a customer types a card into a web form, TLS encrypts it in transit. The gateway decrypts it on arrival. The gateway then tokenises the card and stores the cleartext in its vault — that vault, internally, encrypts the card data at rest. The token comes back to your system, travelling over TLS again. Your CRM never sees the raw card.
You don't pick one over the other. Encryption protects the moments when data has to flow. Tokenisation protects the long stretches when it shouldn't exist in your environment at all. Both are part of PCI DSS control families for a reason.
How Paytia uses both#
Every payment captured through Paytia — phone, in-person, chatbot link, payment portal — moves over TLS to the gateway. The gateway tokenises the card and returns the token, which we store against the customer record. When you charge that customer again for recurring payments, the token travels back over TLS to the gateway, the vault looks up the card, and the transaction goes through. The card itself never enters our systems or yours.
If you want the broader picture, our tokenization explainer walks through the full payment flow, and the tokenization glossary entry has the formal definition. Note: in the US it's spelled "tokenization" — same technology, just orthography. We use UK spelling in most places because we're a UK company, but the SEO traffic mostly comes from the US "z" version.
Pick the right tool for the right problem. Encrypt what has to flow. Tokenise what shouldn't be there.
Related reading#
- Pillar guide: What Is Tokenization And How It Secures Your Data
- What Is a Tokenization Vault? A Plain-English Guide
- Network Tokens vs PSP Tokens: What's the Difference?
- POS Tokenisation Explained: How Card Tokens Work at the Till
Comparing options? Book a 15-minute demo — we'll show you a live capture and quote a real number for your call volume.