A tokenization vault is the secure database, run by a payment processor, that stores real card numbers and hands out tokens in their place. When you take a payment, the gateway puts the card number in the vault and gives you back a token — a meaningless string of characters — that you can store in your own systems. To charge that customer again, you send the token; the gateway looks it up in the vault and processes the real card. You never have the card number, and that's the whole point.
Why vaults exist#
Card numbers are dangerous to hold. PCI DSS treats any system that touches a primary account number as in-scope, which means audits, network segmentation, file-integrity monitoring, quarterly scans — the lot. Most businesses can't afford that cost just to bill a customer twice.
The vault model gets you out of that. The processor (Stripe, Braintree, Adyen, your PSP — whoever you've integrated with) runs a PCI DSS Level 1 environment with the card numbers locked inside it. They give you a reference back. Your CRM, your subscription engine, your accounting system — none of it ever sees the actual card.
What a tokenization vault actually does#
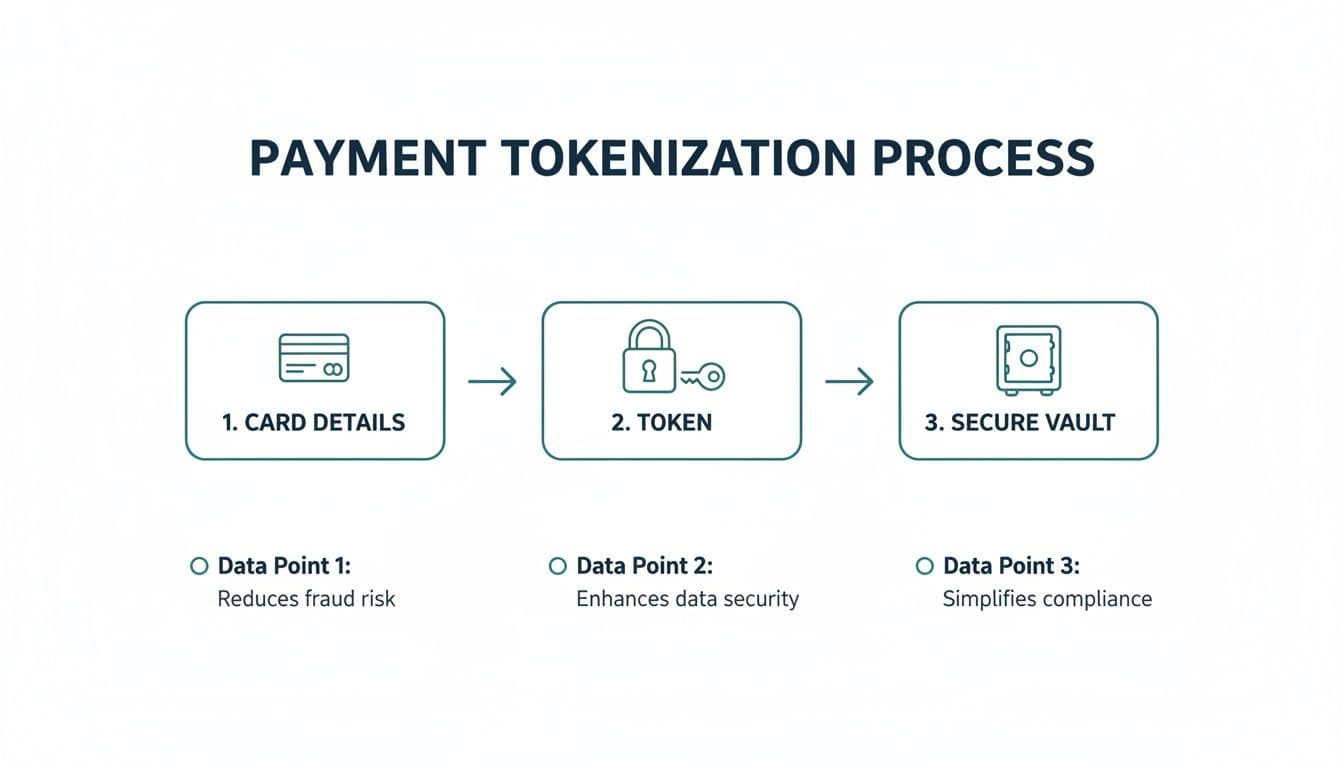
Three things, mostly. First, it stores card data inside a hardened, audited environment so you don't have to. Second, it issues a token — a non-reversible reference that can't be used to reconstruct the card number even if it leaks. Third, it accepts that token back later, looks up the card, and processes the charge.
The token itself has no mathematical relationship to the card number. It's not encrypted card data. It's a lookup key. Lose the vault and you lose the cards — there's no decryption, no recovery from the token alone. That's the security model: the data is gone from your environment, full stop.
Want to see this working in your setup? Book a working-demo call — we'll wire up your actual phone system and show you a live capture.
Where Paytia fits#
We don't run our own vault. The vault is the payment processor's job, and they're better at it than any non-PSP could realistically be. What we do is integrate with the vault on your behalf. When a card is captured through Paytia — over the phone, at a Verifone terminal, via a chatbot link — the data goes straight to the gateway. The gateway returns a token. Paytia stores that token against the customer record so you can charge it again later for recurring payments, deposit balances, and follow-up bookings.
This matters in practice because most teams don't realise the vault is the gateway's, not Paytia's. If you switch gateways, your tokens go with the old gateway — they don't transfer. That's a real consideration if you're picking a processor: token portability between PSPs is rarely clean.
What a vault doesn't protect you from#
A vault stops your systems from holding card numbers. It doesn't stop fraud, chargebacks, or social engineering. If an attacker convinces your team to charge a stored token for a fraudulent order, the vault did its job — the card data was safe — but the money still left. Vault security and transaction-level fraud controls are different problems.
It also doesn't reduce PCI scope to zero by itself. If your call agents read card numbers aloud over an unmuted line, you've put cleartext PAN into your phone system whether or not the vault exists downstream. That's the gap our agent-assisted payments product is designed to close — keypad entry into a tokenised flow, never voice.
When you actually need to think about the vault#
For most merchants, the vault is invisible. You integrate with the gateway, you get back a token, you forget about it. Where it becomes relevant: subscription billing, multi-channel customer journeys, and any scenario where you need to charge the same card across different systems. If that's you, read our primer on tokenization for the broader picture, and the payment tokenisation service glossary entry for how the service layer wraps the vault.
The short version: the vault is a quiet but load-bearing piece of every modern payment stack. You don't run it, but you should understand who does, what their PCI DSS posture looks like, and what happens to your tokens if you ever leave them.
Related reading#
- Pillar guide: What Is Tokenization And How It Secures Your Data
- Network Tokens vs PSP Tokens: What's the Difference?
- Tokenisation vs Encryption: What's the Difference?
- POS Tokenisation Explained: How Card Tokens Work at the Till
Want to see this working in your setup? Book a working-demo call — we'll wire up your actual phone system and show you a live capture.